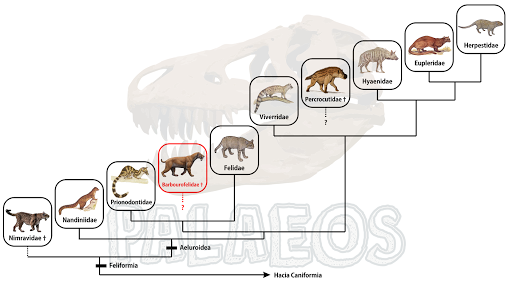
Los barburofélidos son un conjunto de carnívoros (Orden Carnivora) del suborden Feliformia, es decir, forman parte de un conjunto de animales que incluye hoy a félidos, hiénidos, mangostas y otras familias menos sonadas como la Eupleridae, Viverridae, Prionodontidae y Nandiinidae. Los primeros barburofélidos fueron descritos a finales de siglo XIX, pero no fueron reconocidos como un grupo independiente hasta 1970.
A pesar de su reconocimiento como una rama independiente del árbol de los carnívoros feliformes, el misterio más grande del grupo rondaba a su estatus como familia o subfamilia, dentro o fuera de la familia Felidae. Originalmente, fueron descritos como un tipo de félido macaerodontino (subfamilia Machairodontinae), es decir, se pensaba que eran félidos dientes de sable. Posteriormente, fueron transferidos como subfamilia de Nimravidae, un grupo de carnívoros similares a gatos, pero poco relacionados a éstos. Y en 2004 se les asignó a su propia familia, colocándoles de forma cercana a los félidos.
Este esquema de clasificación sin embargo, ha dado un giro en este 2020, pues un nuevo estudio sitúa a los barburofélidos DENTRO de la familia Nimravidae, como una subfammilia (Barbourofelinae). Esto, tras la descripción de una nueva especie: Oriensmilus liupanensis, del Mioceno Medio de China. El nombre de esta criatura significa "escalpelo oriental (o de donde surge el sol) de las Montañas Liupan".
Este es el barburofelino (nueva pronunciación debido a su estatus como subfamilia) más primitivo con caja cerebral intacta descubierto hasta la fecha. ¿Y eso qué tiene de raro? Bueno, pues gracias al basicráneo, se pueden inferir mejor las relaciones de parentesco, pues esta estructura no es moldeada tan fácilmente por el ambiente como para producir convergencias que nublen la identidad de su portador, como es el caso con los barburofelinos.
Por su posición filogenética, Oriensmilus sugiere que el clado de los barburofelinos Europeos y Americanos tienen un origen asiático, lo cual desde luego había sido sugerido antes, por el origen biogeográfico de Sansanosmilus palmidens y estudios previos, pero es bueno ver que estas ideas van cobrando más fuerza dada la nueva evidencia. Y ahora que los barburofelinos son considerados un tipo de nimrávido, su posición filogenética cambia, pues esta familia es considerada como la más primitiva de entre todos los feliformes. Esperemos que esta nueva posición no cambie posteriormente y los pobres vuelvan a quedar "bailando" en la filogenia.
Fuente:
Wang, X., White, S. C., & Guan, J. (2020). A new genus and species of sabretooth, Oriensmilus liupanensis (Barbourofelinae, Nimravidae, Carnivora), from the middle Miocene of China suggests barbourofelines are nimravids, not felids. Journal of Systematic Palaeontology, 18(9), 783-803. https://doi.org/10.1080/14772019.2019.1691066
More info
- Lifestyle Treadmill
- Lifestyle 135
- Curiosidades 7 Pecados Capitales
- Viaje 44 Horas
- Curiosidades Two And A Half
- Curiosidades Plantas
- Why Nirmal Lifestyle Mulund Closed
- Viaje Jet
- Fiesta De 15 Años O Viaje
- Curiosidades Numericas
- Where Is Lifestyle Christianity
- Viaje Resorts
- Viaje 7 Dias Grecia
- Viaje 40 Años
- Curiosidades Musica
- Curiosidades Urso Polar
- Viaje Zombie Red
- Curiosidades Odontologia
- Lifestyle 28 Series Iii
- Viaje Oro Perfecto
- Lifestyle Apparel
- Curiosidades Lingua Portuguesa
- Lifestyle 550
- Lifestyle Trichy
- How Lifestyle Affects The Condition Of The Skin
- Viaje 9 Dias Turquia
- Viaje 800
- Curiosidades Animais
- Is Viajar Regular Or Irregular
- Curiosidades Elite
- Curiosidades Two And A Half
- How Many Lifestyle Stores Are There In India
- Lifestyle Museum
- With Lifestyle Change
- Curiosidades De Plantas Vs Zombies Garden Warfare
- Viaje 2 La Isla Misteriosa Actores
- What Lifestyle Causes Cancer
- Curiosidades Inuteis
- Curiosidades 9 De Julio
- Viaje 6 Dias A Grecia
- 13 Reasons Why Curiosidades
- Viaje De Chihiro
- Lifestyle Galaxy
- Lifestyle App
- Lifestyle Lyrics Amrit Maan
- Viaje Zombie Andre
- Viaje Inmovil
- Curiosidades Que Você Não Sabia
- Can Lifestyle Changes Reverse Hypertension
- Lifestyle Dubai
- Lifestyle 82858
- Viaje Koino Yokan
- Curiosidades Will And Grace
- Curiosidades De 007 Skyfall
- Viaje 94
- 007 Lifestyle
- Lifestyle Zambia
- Lifestyle Museum
- Viaje De Chicas
- Can Lifestyle Have An Effect On Schizophrenia
- Lifestyle 50
- Viaje Translation
- Curiosidades Sobre Two And A Half Man
- Lifestyle Ksa
- Are Un Viaje
- Viaje Entre Regiones Chile
- Viaje Gravedad 0
- Curiosidades 25 De Mayo 1810
- Lifestyle Begumpet
- Viaje 5 Dias Europa
- To Lifestyle In French
- Lifestyle Like A
- Viaje Onirico
- How Many Lifestyle Stores Are There In India
- Curiosidades Um Maluco No Pedaço
- Curiosidades Um Maluco No Pedaço
- Viaje 80 Dias
- Curiosidades Estupidas
- Viaje Usa
- Viaje Meaning In English
- Viaje Way
- Lifestyle Hyderabad
- Viaje Facil Smiles
- Viaje Jet
- Viaje A Las Estrellas
- Are Lifestyle Condoms Durable
- Lifestyle Def
- Viaje Japanese Cigar
- Curiosidades 007 Goldeneye N64
- Is It Love Curiosidades
- How To Say Viaje In English
- Lifestyle Nutrition Vitamin C
- Lifestyle 07
- Spanish Translation For Viaje
- Lifestyle Jaipur
- Viaje 2 La Isla Misteriosa Personajes
- Curiosidades Futebol
- Viaje Por El Mundo
- Curiosidades Urso Polar
- Are Lifestyle Diseases Preventable
- Lifestyle 76
- Fiesta De 15 Años O Viaje
- Lifestyle Xbox Games
- Curiosidades Zoom
- Who Sells Viaje Cigars
- Curiosidades Random